LastMail by LastPass
LastMail by LastPass
Client : LogMeIn ● Date: Nov - May 2018 ● Role: Product Design Lead ● Discipline: Product Design, UX, UI
● Client : LogMeIn
● Date: Nov - May 2018
● Role: Product Design Lead
● Discipline: Product Design, UX, UI
● Client : LogMeIn
● Date: Nov - May 2018
● Role: Product Design Lead
● Discipline: Product Design, UX, UI
● Client : LogMeIn
● Date: Nov - May 2018
● Role: Product Design Lead
● Discipline: Product Design, UX, UI
The Problem
Have you ever tried to buy a home and had to recieve a secure email? The process of sending a secure attachment is easy. Authenticating the receiver of a secure attachment is hard.
Have you ever tried to buy a home and had to recieve a secure email? The process of sending a secure attachment is easy. Authenticating the receiver of a secure attachment is hard.
Have you ever tried to buy a home and had to recieve a secure email?
The process of sending a secure attachment is easy. Authenticating the receiver of a secure attachment is hard.
Have you ever tried to buy a home and had to recieve a secure email? The process of sending a secure attachment
is easy. Authenticating the receiver of
a secure attachment is hard.
It's not obvious how to encrypt an email and most products out there today only solve for the sender while forgeting about
the recievers experience.
It's not obvious how to encrypt an email and most products out there today only solve for the sender while forgeting about the recievers experience.
It's not obvious how to encrypt an email and most products out there today only solve for the sender while forgeting about the recievers experience.
It's not obvious how to encrypt an email and most products out there today only solve for the sender while forgeting about
the recievers experience.
The LastPass team came up with a great idea to solve for email authentication during LogMeIn's Hack week in 2018.
Although they did not win, they put an innovation team together a few months later and I joined as the product designer.
The LastPass team came up with a great idea to solve for email authentication during LogMeIn's Hack week in 2018. Although they did not win, they put an innovation team together a few months later and I joined as the product designer.
The LastPass team came up with a great idea to solve for email authentication during LogMeIn's Hack week in 2018. Although they did not win, they put an innovation team together a few months later and I joined
as the product designer.
We wanted to create the first painless email encryption tool that could be seemless from send to open and we presented
our idea to the executive team.
We wanted to create the first painless email encryption tool that could be seemless from send
to open and we presented our idea to the executive team.
We wanted to create the first painless email encryption tool that could
be seemless from send to open and we presented our idea to the
executive team.
We wanted to create the first painless email encryption tool that could be seemless from send to open and we presented our idea to the executive team.
OUR TEAM WITH DIVERSE SKILLSETS

Solutions exhisting today
HERE IS A SHORT LIST OF SOLUTIONS. THERE ARE A LOT MORE.
There are a number of ways for users today to send and share confidential
information. These are some of the top products out there.

Sending
Sending
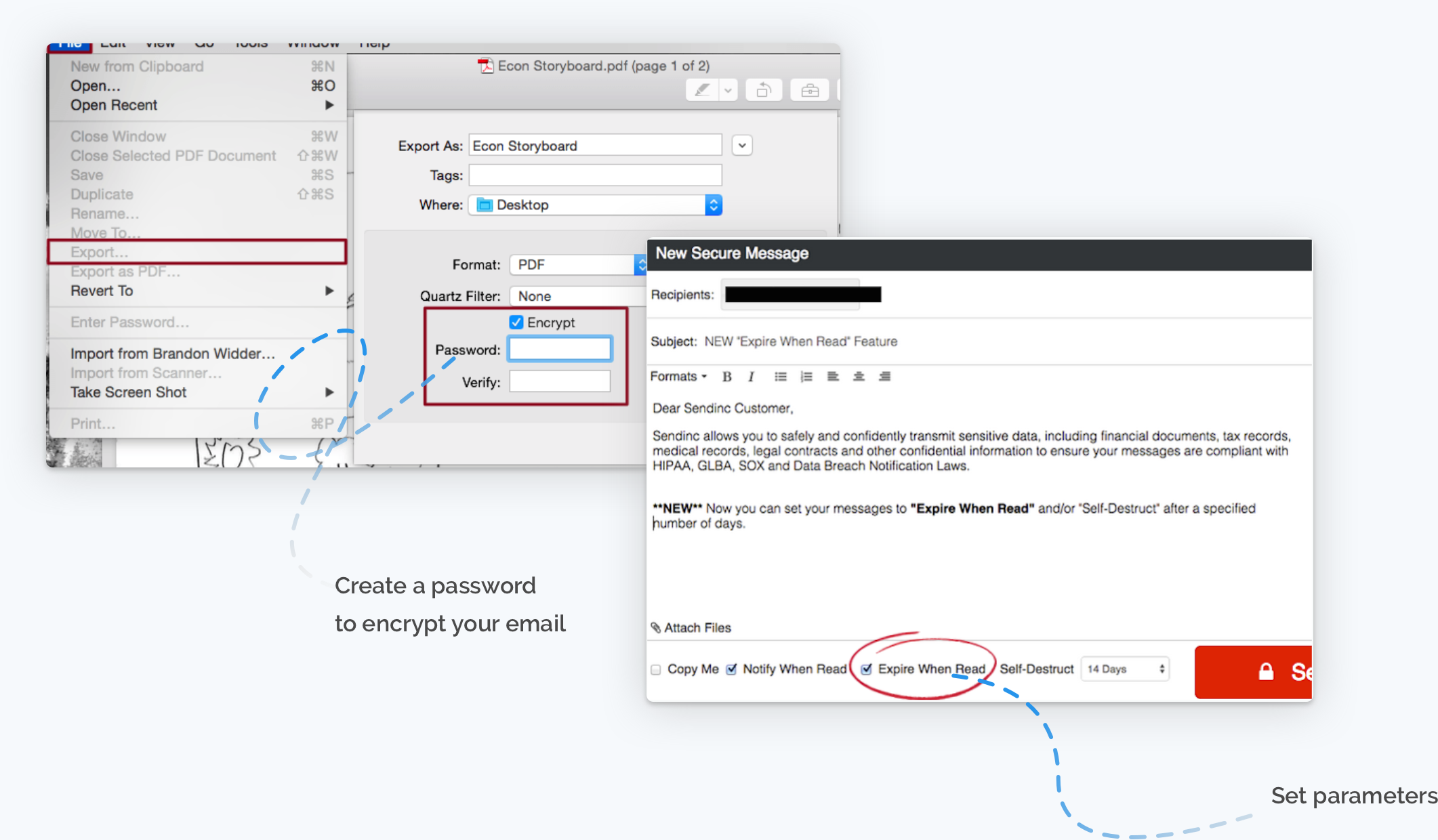
HOW DO WE SOLVE IT TODAY?
It's fairly easy for the sender but with some concerns...
● Create a password to encrypt your email with.
● Create a password to encrypt your email with.
● No validation that the information is actually secure.
● No real way to track if secured attachment was opened.
● 25 MB attachement limits force senders to upload to a cloud file server
● 25 MB attachement limits force senders to upload to
a cloud file server
● Set parameters and send it off.
Recieving
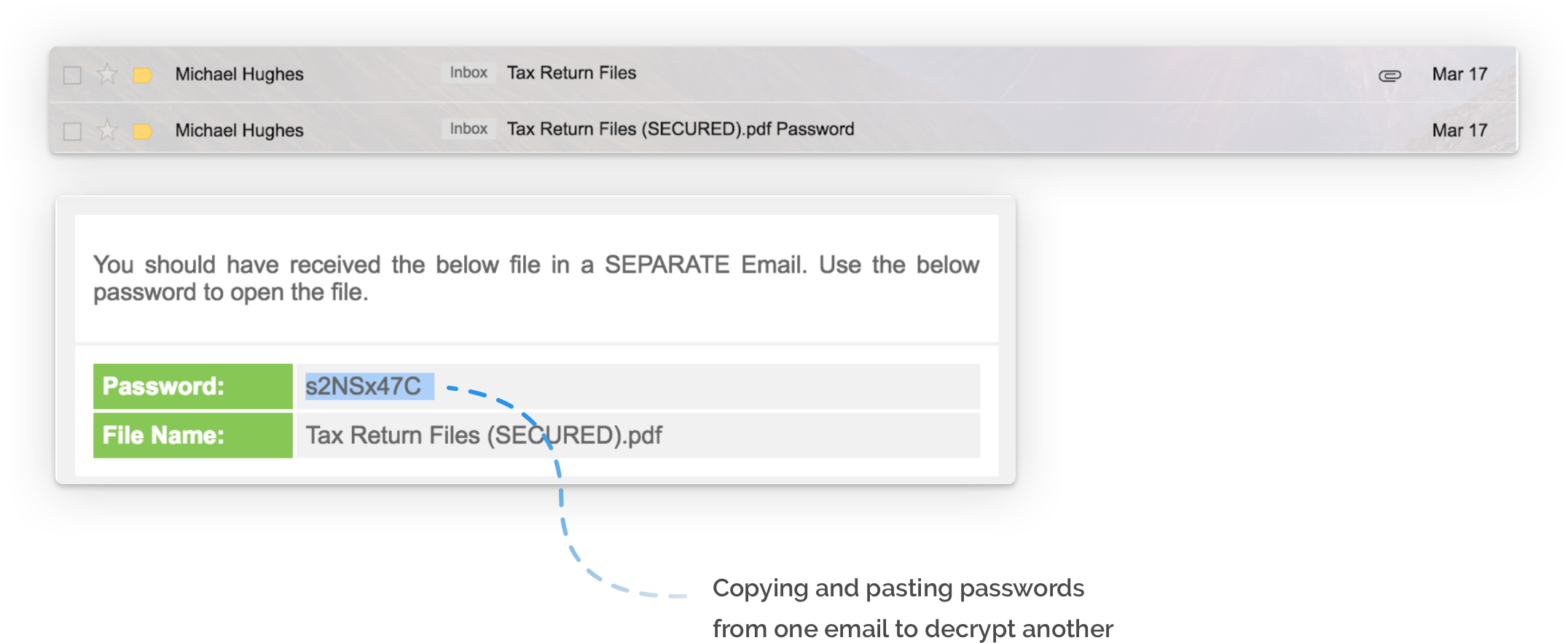
HOW DO WE SOLVE IT TODAY?
It's insecure and the experience is painful.
It's insecure and the experience
is painful.
● Most secure emails need two factor authentication and it's painful for users to figure this out.
● Most secure emails need two factor authentication and it's painful for users to figure this out.
● Most secure emails need two factor authentication and it's painful for users to figure this out.
● Most secure emails need two factor authentication and it's painful
for users to figure this out.
● Most secure emails need two factor authentication and it's painful for users to figure this out.
● Recievers often resort to copying and pasting passwords
from one email into another to authenticate.
● Recievers often resort to copying and pasting passwords
from one email into another to authenticate.
● Recievers often resort to copying and pasting passwords from one email into another to authenticate.
● Recievers often resort to copying and pasting passwords from one email
into another to authenticate.
● Recievers often resort to copying and pasting passwords from one email into another to authenticate.
● Senders often upload to platforms where recievers must
create an account in order to open the file.
● Senders often upload to platforms where recievers must
create an account in order to open the file.
● Senders often upload to platforms where recievers must create an account in order to open the file.
● Senders often upload to platforms where recievers must create
an account in order to open the file.
● Senders often upload to platforms where recievers must create an account in order to open the file.
Archetype
WHAT ARE SOME COMMON CHARACTERISTICS OUR USERS MIGHT SHARE?
Here's an example...
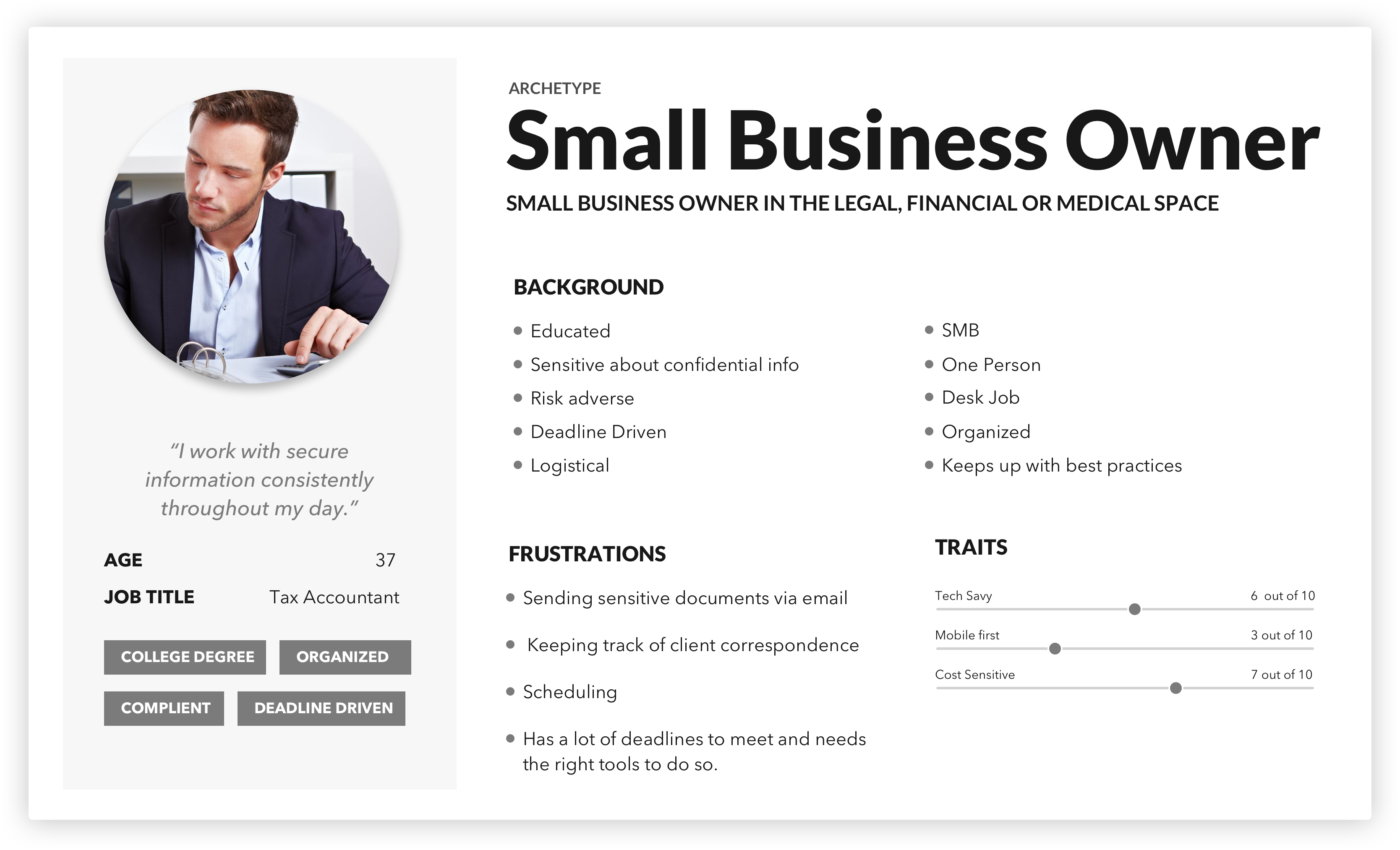
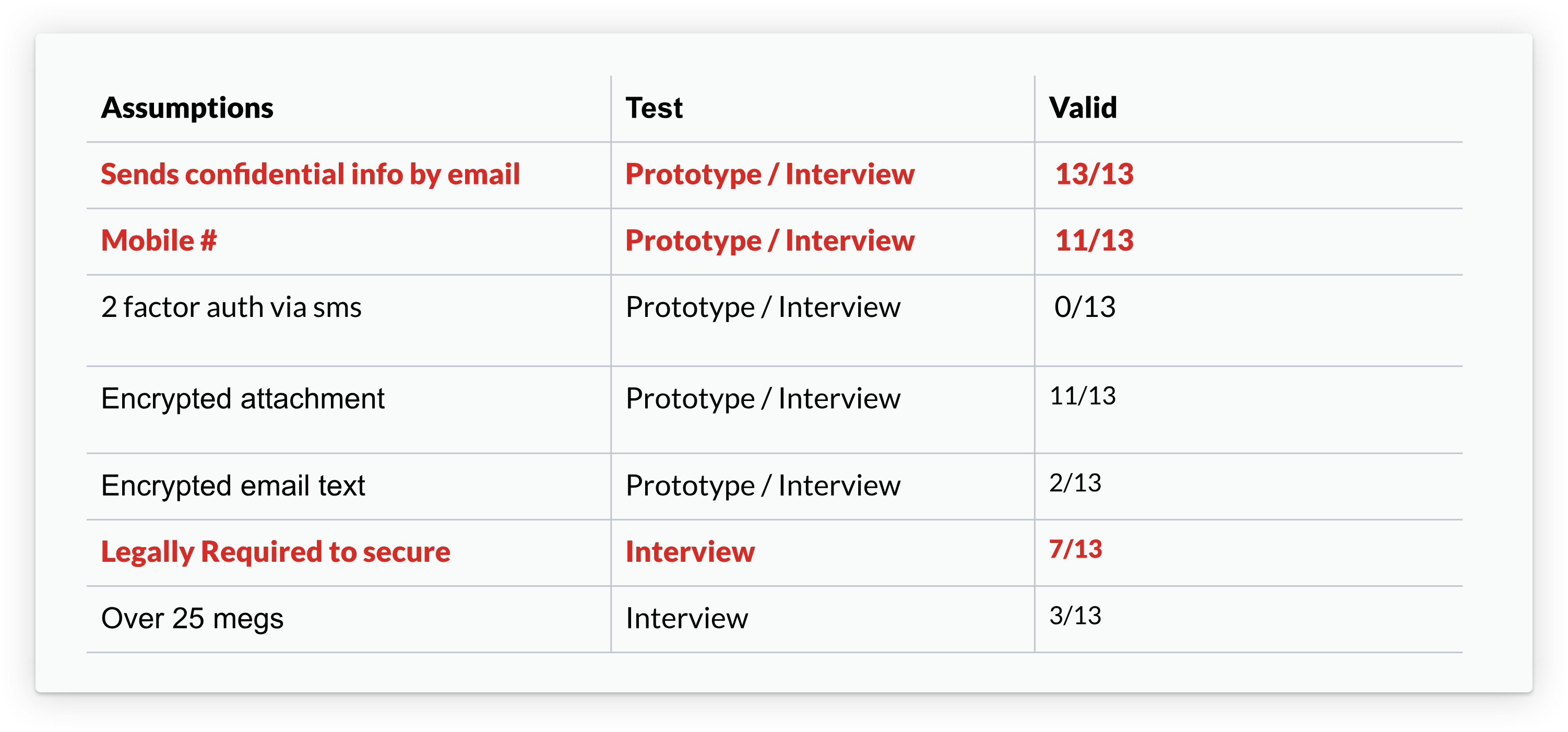
Validating assumptions with real users
After developing an archetype, the team conducted a fact and assumptions exercise to figure out what actions we thought users would need to take in a product like LastMail.
From developing an archetype, the team did a fact and assumptions exercise about what actions
we thought users would need to take in a product like LastMail.
After developing an archetype,
the team conducted a fact and assumptions exercise to figure out what actions we thought users would need to take in a product like LastMail.
Assumption that users...
● Need to send or recieve encrypted attachments
● Need to send or recieve encrypted attachements
● Send confidential info by email
● Send confidential info by email
● Have a mobile number
● Have a mobile number
● Are legally required to secure documents
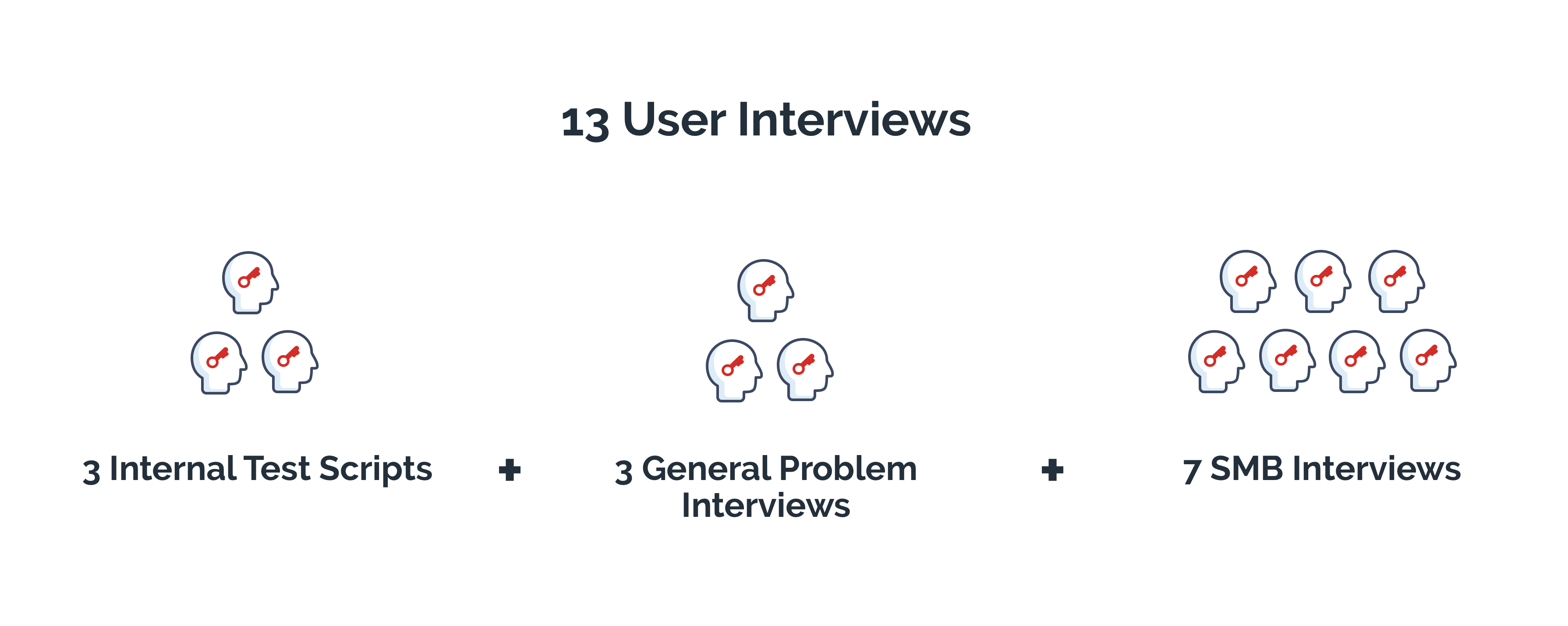
Then we developed an interview script alongside 3 clickable prototypes and started testing the script internally with colleagues
who handle secure information. After initial testing through internal interviews, we branched out and gathered external interviews who fit the archetype.
Then we developed an interview script alongside 3 clickable prototypes and started testing the script internally with colleagues who handle secure information. After initial testing through internal interviews, we branched out and gathered external interviews who fit the archetype.
Then we developed an interview script alongside 3 clickable prototypes and started testing the script internally with colleagues who handle secure information. After initial testing through internal interviews, we branched out and gathered external interviewees who fit the archetype.
Then we developed an interview script alongside 3 clickable prototypes and started testing the script internally with colleagues who handle secure information. After initial testing through internal interviews, we branched out and gathered external interviews who fit the archetype.
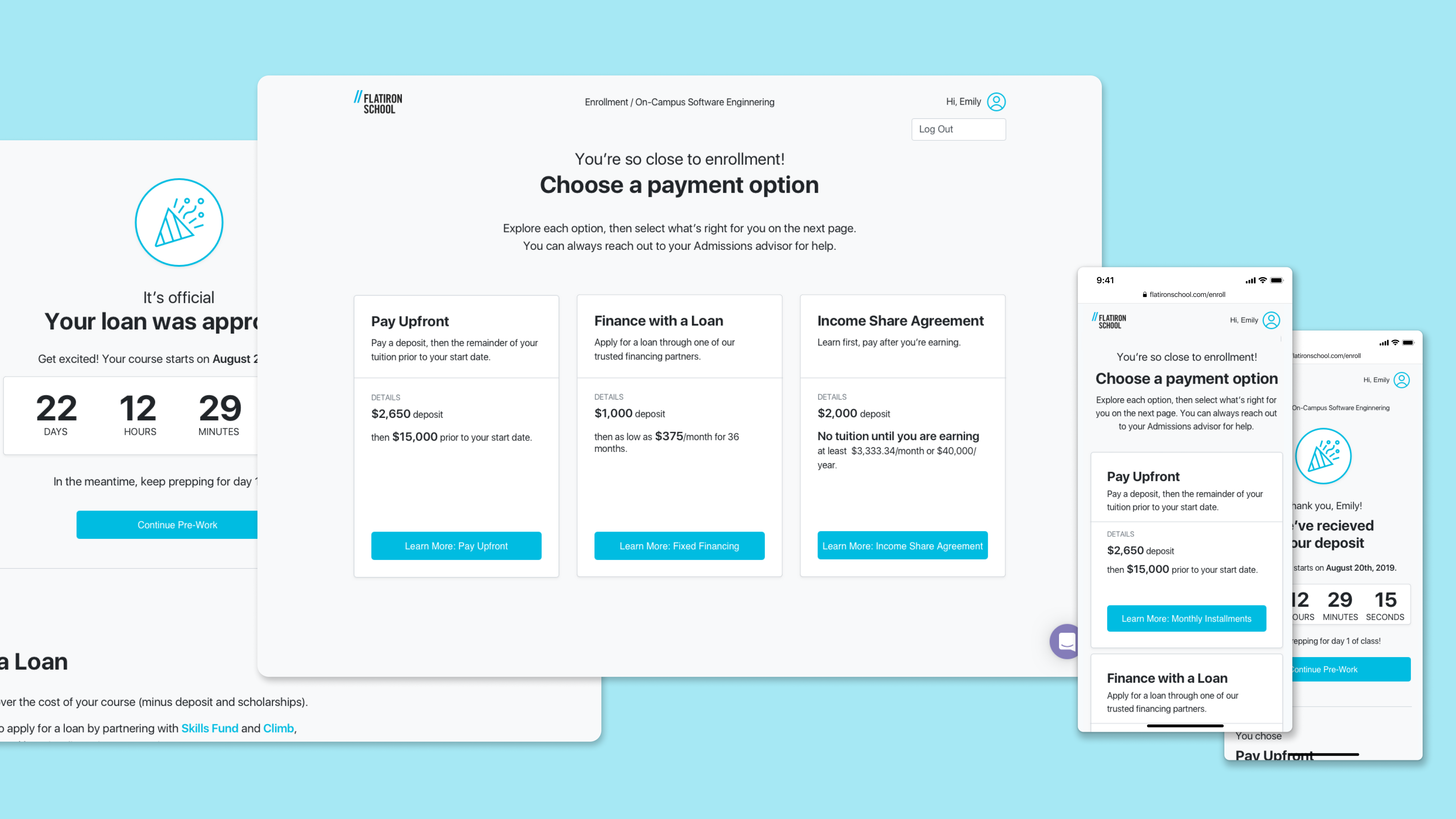
PROTOTYPES
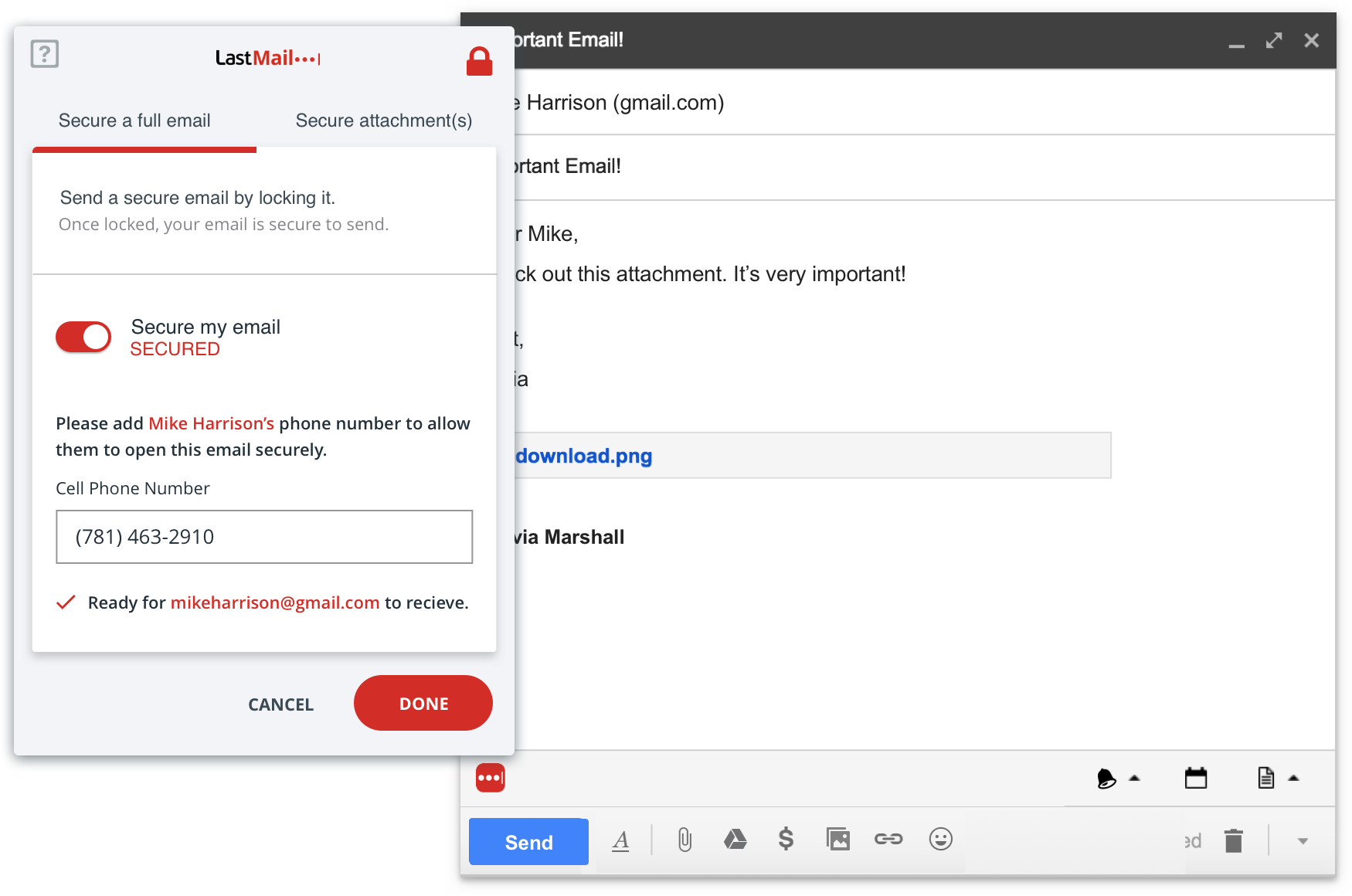
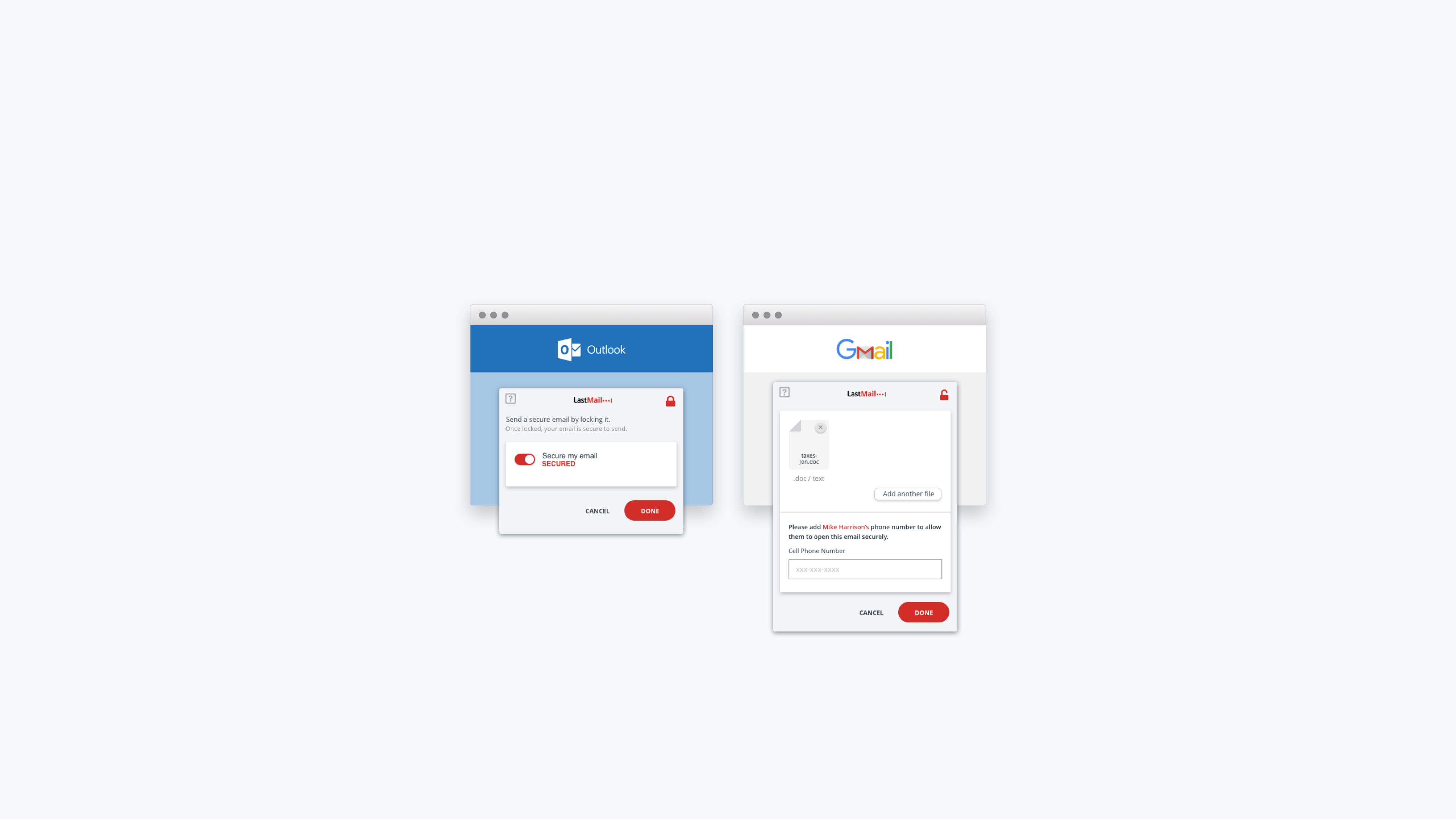
Sending an encrypted email with LastMail
This usecase shows a user choosing the format inwhich they would like to send an encryted email.
They use the recipients phone number to send a 2 factor authentication to their phone to open it.
This usecase shows a user choosing the format inwhich they would like to send an encryted email.
They use the recipients phone number to send a 2 factor authentication to their phone to open it.
This usecase shows a user choosing the format inwhich they would like to send an encryted email.
They use the recipients phone number to send a 2 factor authentication to their phone to open it.
This usecase shows a user choosing the format inwhich they would like
to send an encryted email. They use the recipients phone number to send
a 2 factor authentication to their phone to open it.
This usecase shows a user choosing the format inwhich they would like to send an encryted email. They use the recipients phone number to send a
2 factor authentication to their phone
to open it.
Recieving an encrypted email as a LastMail user
This use-case shows a user opening an encrypted document in an email with their lastmail account. They recieve an email, follow the instructions and open the document seamlessly. When a user is already logged into lastpass on their browser, the decryption
is fast and easy.
This use-case shows a user opening an encrypted document in an email with their lastmail account. They recieve an email, follow the instructions and open the document seamlessly. When a user is already logged into lastpass on their browser, the decryption is fast and easy.
This use-case shows a user opening an encrypted document in an email with their lastmail account. They recieve an email, follow the instructions and open the document seamlessly. When a user is already logged into lastpass on their browser, the decryption is fast and easy.
This usecase shows a user opening an encrypted document in an email with their lastmail account. They recieve an email, follow the instructions and open the document seamlessly. When a user is already logged into lastpass on their browser, the decryption is fast and easy.
Recieving an encrypted email as a non-LastMail user.
This usecase shows a user opening an encrypted document in an email using 2 factor authentication via SMS. They recieve an email, follow the instructions and open the document. Because they don't have a LastPass account, SMS authentication is needed.
User Pain Points
Expressed during interviews on how professionals use encrypted email.
" Sometimes it’s difficult for people who receive the email for the first time, figuring out how to open it and how
to create the password. We have to instruct them in advance on how to do it."
" Sometimes it’s difficult for people who receive the email for the first time, figuring out how to open
it and how to create the password. We have to instruct them in advance on how to do it."
" Sometimes it’s difficult for people who receive the email for the first time, figuring out how to open it and how to create the password. We have to instruct them in advance on how to do it."
" Sometimes it’s difficult for people who receive the email for the first time, figuring out how to open it and how to create the password. We have to instruct them in advance on how to do it."
" Sometimes it’s difficult for people who receive the email for the first time, figuring out how to open it and how
to create the password. We have to instruct them in advance on how to
do it."
HANNAH Taxes
" We have to follow multiple steps and we need to create a dummy account to be able to access the encrypted email.”
" We have to follow multiple steps and we need to create a dummy account to be able to access
the encrypted email.”
" We have to follow multiple steps and we need to create a dummy account to be able
to access the encrypted email.”
" We have to follow multiple steps and we need to create a dummy account
to be able to access the encrypted email.”
AJ Marketing & Advertising
"A lot of the times someone will download the document and we’ll give them instructions but they don’t do it at that time and we end up needing to schedule a call to open the document.”
"A lot of the times someone will download the document and we’ll give them instructions but they don’t
do it at that time and we end up needing to schedule a call to open the document.”
"A lot of the times someone will download the document and we’ll give them instructions but they don’t do it at that time and we end up needing to schedule a call to open the document.”
JOHN Investment Management
Reactions to LastMail
Expressed while walking through clickable prototypes
"I love that I don’t have to go to a different website. I don’t have to leave Gmail. It’s awesome!"
"I love that I don’t have to go to a different website. I don’t have to leave Gmail.
It’s awesome!"
"I love that I don’t have to go to a different website.
I don’t have to leave Gmail. It’s awesome!"
SEYMONE Telecommunications
"LastPass is adding two-factor authentication, which I like, essentially we are kind of doing that, we usually send an email with a password, a separate email. This you’re kind of removing that step and having it sent via text message, which I like better.”
"LastPass is adding two-factor authentication, which I like, essentially we are kind
of doing that, we usually send an email with a password, a separate email. This you’re kind of removing that step and having it sent via text message, which I like better.”
RYAN Information Technology
LastMail today
Our innovation team was asked to pitch our findings, prototypes and concept to the executive team at LogMeIn. The goal was to get buy in for the 90 day LogMeIn incubator program. We were hoping to convince the executive team to sponsor the build of a stand alone MVP for LastMail to validate a product market fit by converting free LastPass users to paid users.
Ultimately the pitch fell short, as the executive team did not see enough of a potential product market fit in the end. The exercise
to push our team to think outside the box and explore a new market avenue for Lastpass was priceless. See our pitch deck here.
Ultimately the pitch fell short, as the executive team did not see enough of a potential product market fit in the end.
The exercise to push our team to think outside the box and explore a new market avenue for Lastpass was priceless.
See our pitch deck here.
Ultimately the pitch fell short, as the executive team did not see enough of a potential product market fit in the end. The exercise to push our team to think outside the box and explore a new market avenue for Lastpass was priceless. See our pitch deck here.
Ultimately the pitch fell short, as the executive team did not see enough
of a potential product market fit in the end. The exercise to push our team to think outside the box and explore a new market avenue for Lastpass
was priceless. See our pitch deck here.
Ultimately the pitch fell short, as the executive team did not see enough of a potential product market fit in the end. The exercise to push our team to think outside the box and explore a new market avenue for Lastpass was priceless. See our pitch deck here.
Hey there, this is the default text for a new paragraph. Feel free to edit this paragraph by clicking on the yellow edit icon. After you are done just click on the yellow checkmark button on the top right. Have Fun!
FlatIron School AdmissionsProduct Design
LastMail by LastPassProduct Design
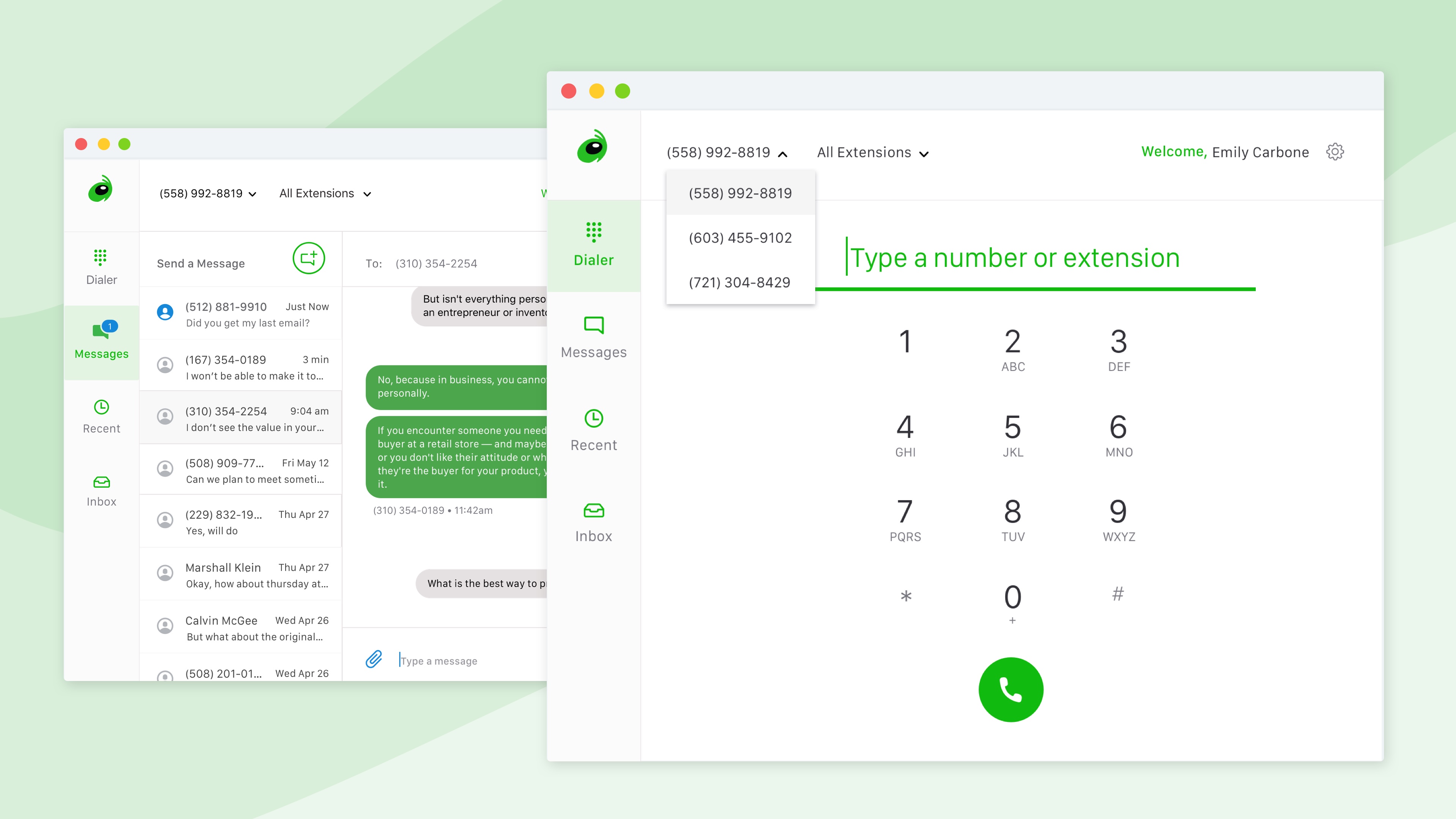
Grasshopper for DesktopProject type
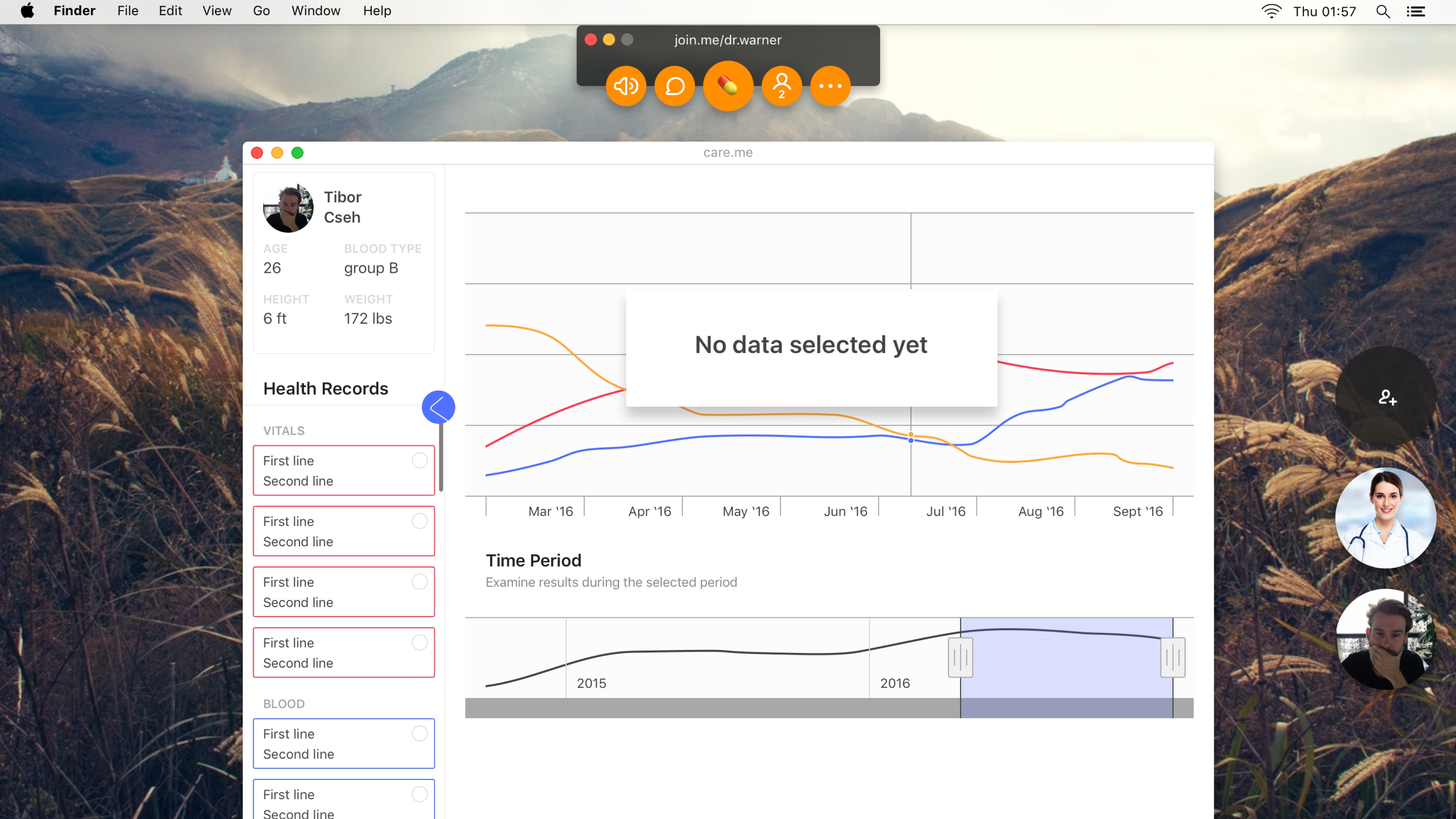
care.meProduct Design
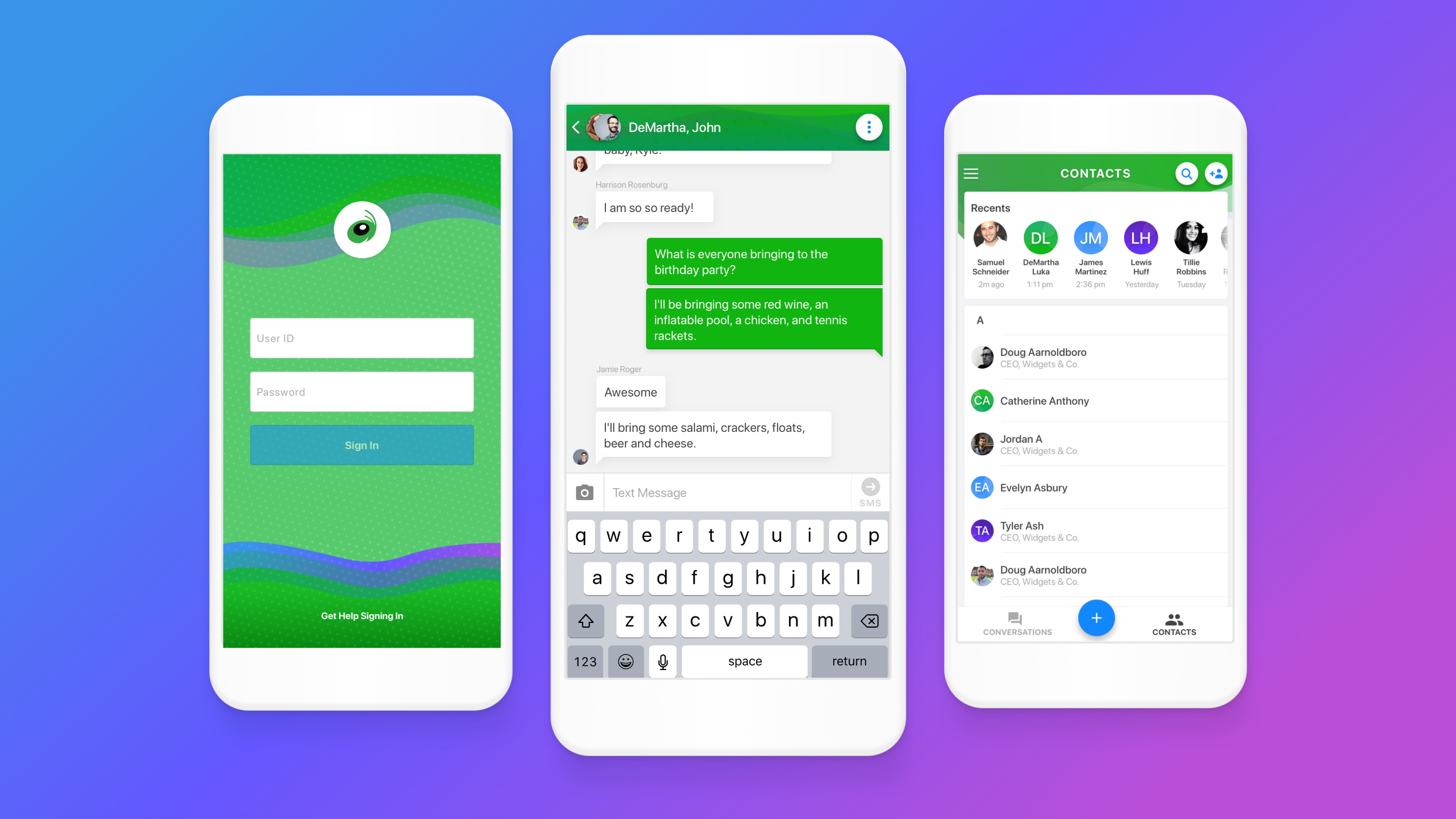
Connect Mobile AppProduct Design
The Four Pillars of CollaborationPublic Speaking
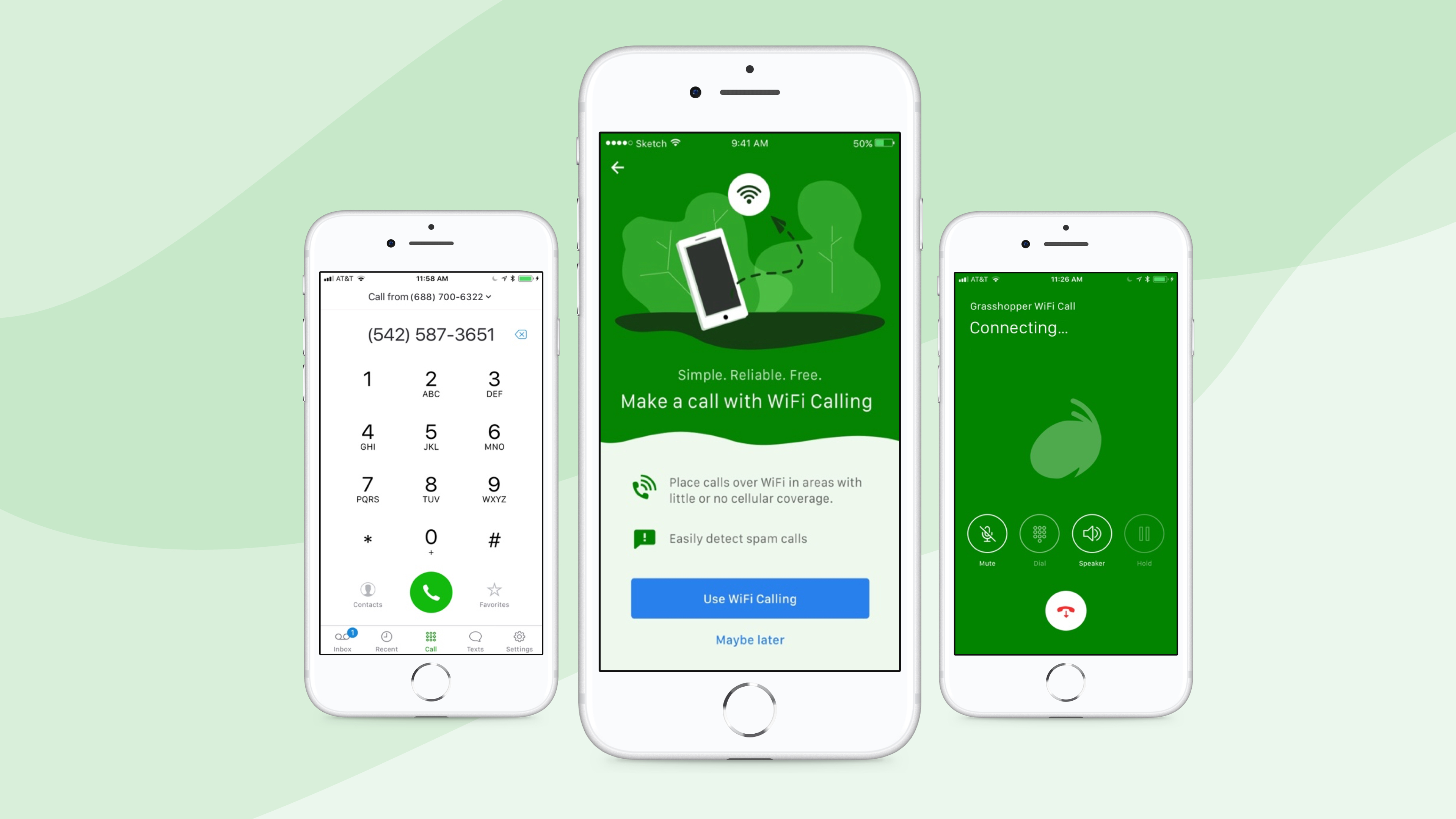
Grasshopper WiFi CallingProduct Design
Homepage Marketing TestRedesign

KodeConnectPrint Design
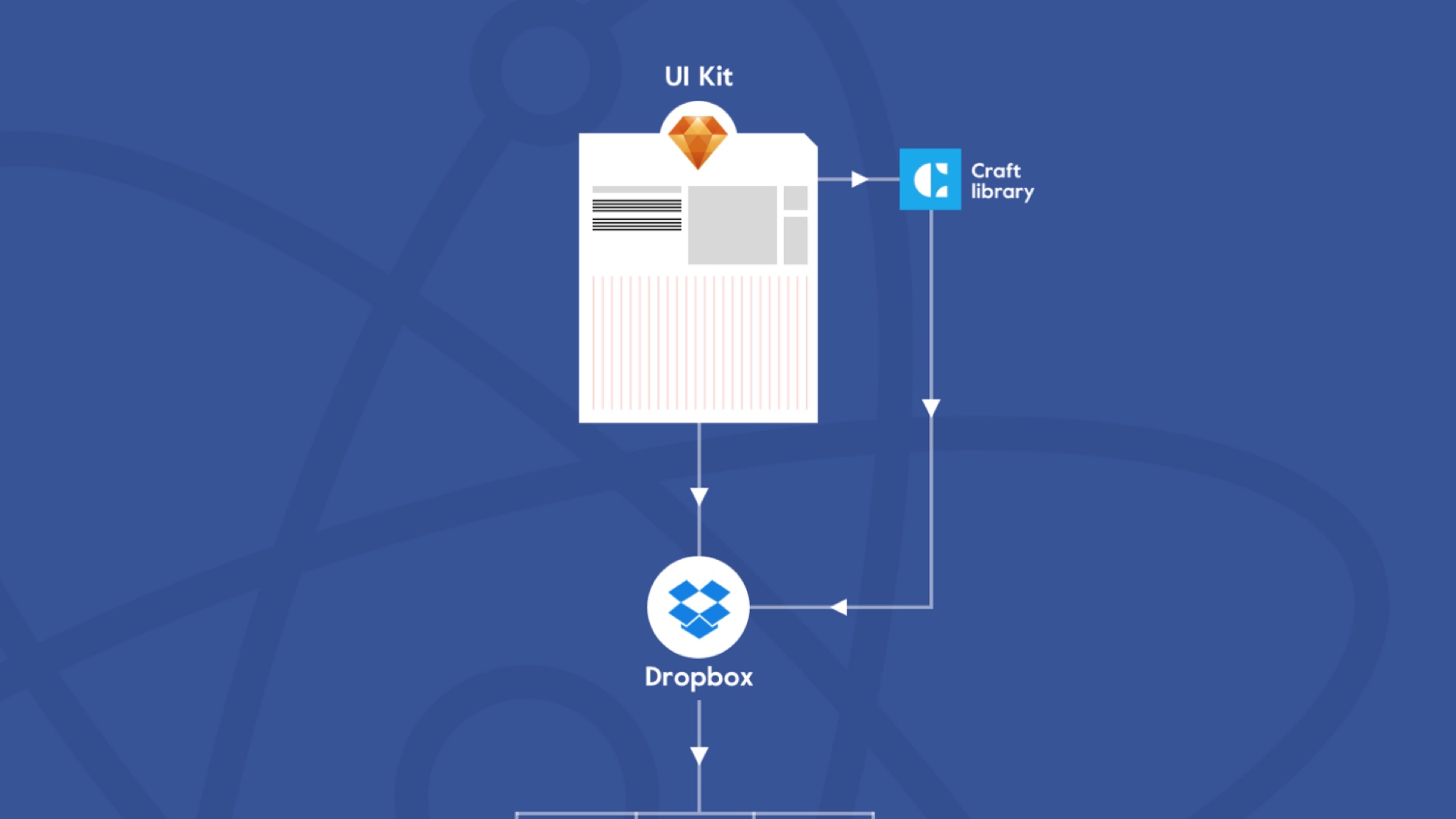
Building a Cross Product Design SystemDesign Systems
Xively + SalesforceProduct Design
Thanks for viewing my site!
Email me at lizharrisdesign@gmail.com
or follow me on social media!
Thanks for viewing my site!
Email me at lizharrisdesign@gmail.com
or follow me on social media!
Thanks for viewing my site!
Email me at lizharrisdesign@gmail.com
or follow me on social media!